Integrate Zero Trust concepts into Remote Privileged Access Management
Resource reservation
Thinfinity's Resource Reservation Module offers a tailored approach for providing temporary remote application access to employees, contractors, and vendors. It facilitates the creation of custom bookable access profiles, which can be configured through the Thinfinity Resource Reservation interface, ensuring a personalized and secure access management system.
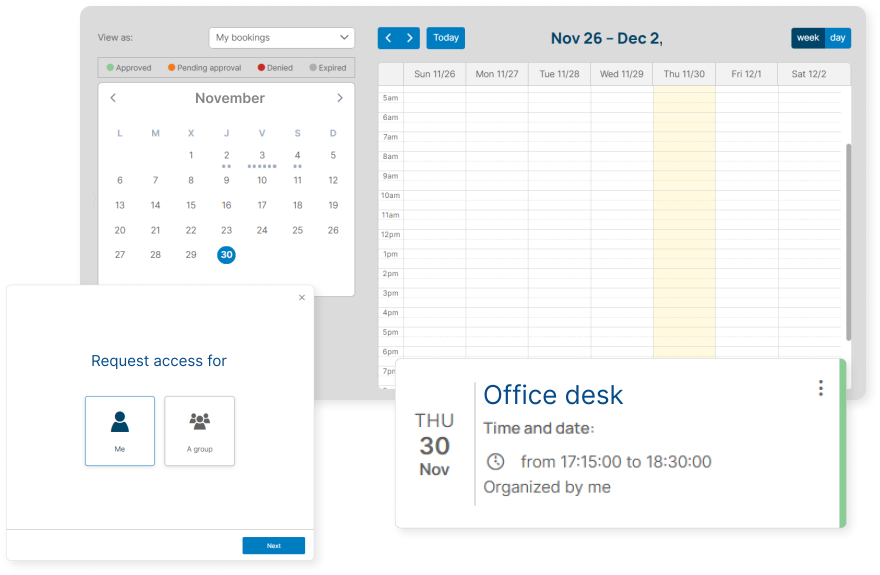
Streamline processes with Thinfinity's approval workflows
Customizable workflow design
Provides the capability to customize approval workflows to align with unique organizational requirements, accommodating various role types such as administrators, users, and supervisors.
Audit trail and compliance
Ensures a complete audit trail of approvals for compliance purposes, providing transparency and accountability in access management.
Automated approval requests
Facilitates quick and efficient handling of access requests with automated workflow mechanisms.
Multi-level approval system
Supports complex, multi-tiered approval processes for enhanced security and control over access permissions.
Real-time notifications
Keeps relevant parties informed with instant notifications in portal and by email on approval requests and decisions.
Use cases

Temporary and Time Based Access for Employees
Incorporates efficient approval processes for temporary access requests, ensuring quick and secure authentication.
Core features
Preferred by teams globally for ensuring secure access
Secure remote access
Enable secure, fluid connections to vital IT frameworks, cloud services, and OT systems from any location, without relying on VPNs.
Session management
Attain complete oversight and command over every action, permission, and more in each privileged session. Compliance is effortlessly achieved with intricate documentation of every session, meticulously recorded and stored.
Privileged access control
Apply least privilege and just-in-time principles by providing users with the precise level of remote access necessary, limited to the exact time required.
Real time monitoring and alerts
Monitor privileged activities in real-time with an advanced system that alerts administrators to unusual activities, enhancing security response.
Streamlined authentication
Enhance efficiency and system security with multi-factor, passwordless, and SAML authentications, streamlined for easy integration and access.
Compliance & session auditing
Achieve readiness for SOC 2 compliance with detailed session audits, forensic analysis, and advanced analytics, drawing from comprehensive session data available both immediately and after the fact.
Product highlights
Deployment optionsSimplify access for end users
Privileged Remote Access enables a smooth user experience that empowers users to work with the tools they want. By brokering all connections through a single, secure access pathway, your attack surface is significantly reduced. Oversight and auditing are also simplified by getting a single list of authorized endpoints available for each user.
Zero Trust Architecture (ZTA)
Aligned with zero trust principles, Thinfinity's solution ensures that all access across the enterprise is justified, properly scaled and meticulously documented. It allows for just-in-time access tailored for internal teams, external vendors, and OT systems, using detailed least privilege access controls.
Gain complete oversight of remote access
Streamline remote session management using Thinfinity's centralized platform, compatible with a wide array of protocols: RDP, VNC, HTTPS, SSH, SQL, Webdav, WAG, TN3250, TN5250, Thinfinity VNC, and VirtualUI. Administrators have complete control over session scheduling, user access, and application permissions, along with the ability to capture and review session data.