
Our online terminal emulator client solution combines the security of a centrally-managed server with the accessibility of web-based clients that any HTML5 browser user can launch.
Browser-based solutions work with virtually any device now, and often require single sign-on or other authentication measures.
The present article covers the configuration of Centrify SSO with SAML for z/Scope Anywhere Web Terminal Emulator.
TIP: Not sure what’s the best SSO solution for your Mainframe/iSeries host? Contact us to get advise.
How to configure SAML to enable Centrify
On the Centrify’s Admin Portal.
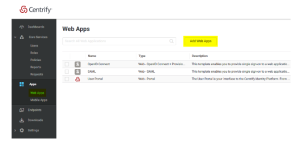
1) Click on “Apps” -> “Web Apps”:
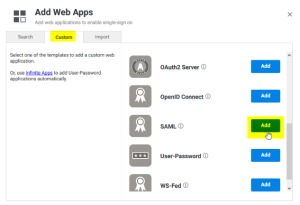
2) Click on “Custom” and next to SAML, press “Add”:
3) Give your application a name, and click on the “Trust” tab.
Click on “Manual Configuration”, and copy the IdP Entity ID, and download the certificate provided by Centrify.

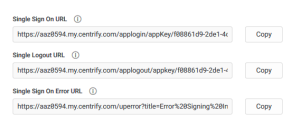
4) Then copy the “Single Sign-on URL”, and the “Single Logout URL”:
5) Now, on the “Service Provide Configuration”, click on “Manual Configuration” and configure the following:
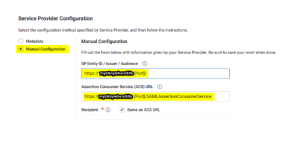
After doing these changes, click on the “Save” button.
6) Now we need to configure your z/Scope Anywhere Server with all this information.
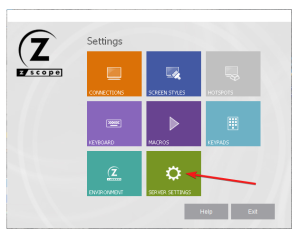
Open the z/Anywhere Server Manager and click on “Server Settings”.
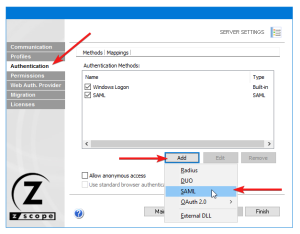
Then, navigate to the “Authentication” tab, press “Add”, and then SAML:
7) Now we must configure the connection itself:

Service identifier = https://YourThinfinitySite:[Port]
Service Cert File = [Path_To_Your_Certificate]
Service Cert Pass = [Certificate_Password]
Identification Entity = [IdP Entity ID / Issuer]
Single Sing on Service URL = [Single Sign on URL]
Sign-out URL = [Single Logout URL]
Partnet Cert File = [Certificate Provided by Centrify]
Once you configured it properly, click “Ok” to save the changes.
8) Now go the online terminal emulation landing page and you should see the “Login with SAML” option now available to use.

Have any questions? Contact us at [email protected] or leave a message on this same post.
Quick Tip: Learn how to configure Duo Security Login to access to Mainframe and AS/400 Hosts.